EdgeWave iPrism Deployment
Comprehensive, policy-driven Web Security
A Powerful Internet Security Appliance
The iPrism Web Security delivers comprehensive, policy-driven Web Security by combining software flexibility and scalability with the security and control of an network security appliance based solution. The iPrism h-Series Web security appliance is designed to enhance iPrism's capabilities now as well as prepare for new features and functionality in the future.
Secure Content Management for the Enterprise
EdgeWave introduces our newest appliance, the 500h, built to handle the size and bandwidth requirements of a large enterprise or any organization that wants to manage Web access in a bandwidth-intensive environment.
Network Security Appliances Fit
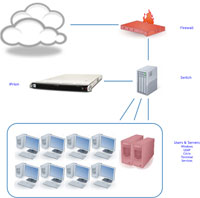
iPrism Web Security offers flexible deployment options in an Internet security appliance that fits into a wide variety of network platforms and configurations. The iPrism Web Security Appliance can scale from small to large enterprise networks and delivers unrivalled performance in both distributed and centralized networks as well as mixed environments, including Terminal Services.
Transparent Bridge Deployment of iPrism Web Security Appliance
Our exclusive transparent bridge deployment allows the iPrism Internet security appliance to delivers powerful Web security that won't introduce latency to your network traffic no matter how busy your network gets. Even networks with the largest pipelines are easily managed by our combination of seamless in-line deployment or iPrism network security appliances and the exclusive kernel-level filtering technology.
Terminal Services
If you're a Citrix user, your environment can cause special challenges when you need to deploy an Internet filtering solution. Recent tests conducted by Citrix engineers confirm that the iPrism Web Security solution surpasses all competitors in its ability to easily integrate within a Citrix environment without degrading performance. That's why Citrix has proclaimed our solution the only Citrix Ready appliance-based Web Filter on the market.
Remote Filtering
iPrism Web Security offers a Hybrid Remote Filter that employs proprietary technology to bring powerful Web filtering to all your users, regardless of their location, without using your VPN, deploying anything in the DMZ or requiring any PAC file implementations. iPrism Web Security eliminates browser latency while delivering secure and comprehensive Web access management to all your off-premises users.
Comprehensive Email and Web Security Appliance Solutions
EdgeWave offers comprehensive security solutions including both email and web security appliance based products. The ePrism Email Security Suite offers in-the-cloud protection against spam, data loss, and compliance violations.
Hardware Overview:
iPrism's powerful h-Series appliances are offered in models to fit a wide range of requirements. iPrism Web Security delivers comprehensive, policy-driven Web Security by combining software flexibility and scalability with the security and control of an appliance-based solution. The cost-efficient iPrism SMB h-Series appliances are designed to enhance iPrism Web Security capabilities now as well as prepare for new features and functionality in the future.
The compact, 1U, h-Series appliances are compatible with all supported versions of the iPrism Web Security operating software and deliver throughput speeds ranging from 10 to 30 Mbps depending on the model you choose. With a variety of models available to suit your requirements, the iPrism Web Security is designed to fit any size organization. The iPrism Web Security, delivered via the h-Series appliances, provides powerful, comprehensive Web Security to organizations ranging from large enterprises to small and medium-sized businesses.
SMB h-Series Appliances
iPrism 15h
The iPrism 15h delivers superior Web Security results to small organizations and includes the same hardened and optimized OS, high-performance components and ease-of-use you have come to expect from the iPrism Web Security. The 15h is ideal for organizations with 1-175 workstations, although other factors such as high Web usage activity, longer access event retention and bandwidth are also important points to consider when choosing the right model for your organization. If you are looking for network failover capabilities, consider upgrading to the 25h.
iPrism 25h
The iPrism 25h is the model that comes after the 15h and includes more processing power and a 1 Gbps network failover card for added reliability. It is an ideal choice to handle the Web Security needs of small and medium-sized organizations that have greater bandwidth or access event retention requirements. If you are looking for a server-grade appliance with redundant power supplies and hard drives, consider upgrading to the 35h.
iPrism 35h
The iPrism 35h is the next step after the 25h but it represents a leap in processing power, hard drive space and server-grade features to handle more users, longer access event retention and a bigger pipeline. If you need more Web Security speed, consider the 55h or 105h models.
| Appliance | Model: | 15h | 25h | 35h |
|---|---|---|---|---|
| Performance | Unfiltered Traffic Throughput |
Up to 1 Gbps | ||
| Filtered Traffic Throughput |
10+ Mbps | 20+ Mbps | 30+ Mbps | |
| Transactions per Second 1 | 160+ | 300+ | 400+ | |
| Access Event Records Retained 2 |
114 million | 320 million | ||
| Number of Workstations |
up to 175 | up to 500 | up to 1,000 | |
| Hardware Specifications |
Processor | Atom D525 1.8GHz/1MB | Core i3-540 3.06GHz/3MB | |
| Memory | 2GB DDR3 | 4GB DDR3 | 4GB UDIMM ECC DDR3 1333 | |
| Disk Drives & RAID Controller | 500GB SATA | 2 X 500GB SATA Drives 9650SE-2LP Raid Card |
||
| Ethernet Interface | 2 x 10/100/1000 Management NIC |
2 x 10/100/1000 Management NIC with 2 x 10/100/1000 Full Duplex Interfaces with BYPASS circuit |
||
| LCD Panel | NA | DB631-Bk-TMF-KU | ||
| Physical Specifications |
Form Factor, Dimensions & Weight |
1U height, rack-mountable w/o rails 1.75"(H) x 14"(W) x 16.7"(D) @ 15 lbs |
1U height, rack-mountable w/ rails 1.75"(H) x 16.8" (W) x 25.6"(D) @ 40 lbs |
|
| Power | Single Supply with 115-230 VAC @ 50-60 Hz and 4.0A @115V (200W) |
Dual Hot-Swap Supplies with 100-240 VAC @ 50-60 Hz and 4.0-8.0A@115V (450W) |
||
| Heat Output & Operating Temperature | 1320 BTU per hour (max.) and 10° to 35°C (50° to 95°F) |
1850 BTU per hour (max.) and 10° to 35°C (50° to 95°F) |
||
Large Enterprise h-Series Appliances
iPrism 55h
The iPrism 55h is the next model after the 35h and represents a significant upgrade in power. Like the 30h, the 55h is a full 1U chassis with the 1 Gbps failover NIC, dual hot-swap power supplies and hard drives it is capable of handling medium to large-sized small enterprises with high-speed pipelines. If you are looking for an even faster Web Security experience, consider our most powerful appliance, the 105h.
iPrism 105h
The iPrism 105h doubles the processing cores and hard drive storage, for more throughput and access event retention. It is capable of handling medium enterprises with large pipelines.
iPrism 500h
Like all iPrism's h-Series high-performance appliances, the 500h is a completely self-contained solution with its own hardened and optimized OS. The 500h handles large enterprise, bandwidth heavy environments, or organizations that need to retain access events for a long time for compliance. It does not rely on legacy solutions to control bandwidth such as a caching proxy. These legacy approaches are not only less effective, they lack the scalability that can accommodate you as your organization and/or bandwidth requirements grow.
| Appliance | Model: | 55h | 105h | 500h |
|---|---|---|---|---|
| Performance | Unfiltered Traffic Throughput |
Up to 1 Gbps | ||
| Filtered Traffic Throughput |
50+ Mbps | 100+ Mbps | 500+ Mbps | |
| Transactions per Second1 | 600+ | 1,300+ | 6,000+ | |
| Access Event Records Retained2 |
320 million | 790 million | 2 billion | |
| Number of Workstations |
up to 2,500 | up to 10,000 | up to 20,000 | |
| Hardware Specifications |
Processor | Intel Quad-Core Xeon X3430 2.4GHz/8MB |
Intel Quad-Core Xeon X3470 2.93GHz/8MB |
Dual Intel Quad-Core Xeon 3.46GHz/12MB |
| Memory | 4GB Reg ECC DDR3 | 6GB ECC DDR3 | ||
| Disk Drives & RAID Controller | 2 X 500GB SATA Drives 9650SE-2LP Raid Card |
2 X 1 TB Hot-Swap SATA with RAID 1 (Mirrored) |
2 X 2 TB Hot-Swap SATA with RAID 1 (Mirrored) |
|
| Ethernet Interface | 2 x 10/100/1000 Management NIC with 2 x 10/100/1000 Full Duplex Interfaces with BYPASS circuit |
|||
| LCD Panel | DB631-Bk-TMF-KU | NA | ||
| Physical Specifications |
Form Factor, Dimensions & Weight |
1U height, rack-mountable w/ rails 1.75"(H) x 16.8" (W) x 25.6"(D) @ 40 lbs |
2U height, rack-mountable w/ rails 3.5"(H) x 17.2" (W) x 25.6" (D) @ 50 lbs |
|
| Power | Dual Hot-Swap Supplies with 100-240 VAC @ 50-60 Hz and 4.0-8.0A@115V (450W) | |||
| Heat Output & Operating Temperature | 1850 BTU per hour (max.) and 10° to 35°C (50° to 95°F) | |||
Network Fit:
iPrism Web Security simply fits in networks of all shapes and sizes.
- Scales both large and small.
- Distributed or centralized.
- Mixed networks including Terminal Services.
Transparent Bridge:
Our exclusive transparent bridge deployment delivers powerful Web security that won't introduce latency to your network traffic no matter how busy your network gets. Even networks with the largest pipelines are easily managed by our combination of seamless in-line deployment and kernel-level filtering technology.
Installing an iPrism Web Security appliance in its typical Transparent Bridge Mode has several benefits:
- It combines the accuracy and security of pass-through filters with the speed of a pass-by or sniffer-type solution, giving you the best of both worlds:
- Pass-thru traffic is securely monitored defeating any attempts to circumvent the Web filter
- Pass-by traffic is picked up and pages are blocked according to your organization's policies
- Kernel-level filtering means the appliance is not acting in proxy mode and latency is never introduced into the process
- Flexible transparent deployment means the EdgeWave Web Security appliance can still function as a direct proxy when deployed in Transparent Bridge Mode.
- Functioning in both modes simultaneously allows greater flexibility in deployment.
- Proxy functionality is available for multi-user workstations or as an alternative to our Remote Filtering solution for remote users who may not use the same gateway to the Internet as on-site users
- Because all traffic flows over the Transparent Bridge, features and functionality that take advantage of this visibility can be easily downloaded to the Web filter
- Single Point of Failure issues are eliminated with the Bypass Module on the NIC because any problems with the Web filter will not affect normal network operations or performance
- As a stand alone appliance with no additional software or servers required, iPrism Web Security has greater flexibility in adapting to a wide range of network scenarios involving mixed platforms, legacy systems and other variants
Terminal Services:
If you're a Citrix user, your environment can cause special challenges when you need to deploy an Internet filtering solution. Recent tests conducted by Citrix engineers confirm that the iPrism Web Security solution surpasses all competitors in its ability to easily integrate within a Citrix environment without degrading performance. That's why Citrix has proclaimed our solution the only Citrix Ready appliance-based Web Filter on the market.
iPrism Web Security Offers Significant Advantages in Citrix Environments
Citrix Partner - Citrix Ready One of the main reasons that iPrism Web Security is the only Citrix Ready appliance based Web filter and ideal for your Citrix environment is our unique auto-login feature. When this feature is deployed, users are allowed to maintain their productivity without incessant authentication requests. This ensures that uniform policy application and enforcement are being enabled across your organization.
- Our unique "session based" authentication technology allows you to use Auto-login and greatly simplify the authentication process
- Our technology allows Citrix users to easily apply unique policies to individual users and document their activity
- This authentication feature is enabled without installing any software on the Citrix or AD servers
- Our technology ensures consistent policy application whether Citrix users are Web surfing from their desktop or via Citrix systems
- If you require more aggressive security because of the shared nature of terminal server clients, you can easily configure iPrism Web Security to require manual authentication.
Deploying iPrism Web Security in a Citrix Environment is easy
It only takes a few steps to install iPrism Web Security in your Citrix environment:
- Install our appliance upstream of your Citrix server, and inline with your Firewall
- Create profiles and policies in the Appliance Manager
- Enable auto-login
- Establish session-based authentication for Citrix
- Block, monitor and report on all thin/fat client use
iPrism Web Security Offers 5-Star Features
- Antivirus - Includes a powerful, four-factored antivirus engine at no extra charge
- IM and P2P protocol management
- Spyware, malware and phishing blocking (hourly updates)
- Comprehensive drill-down own reporting and real-time monitoring
- Authentication - Active Directory and LDAP Authentication simplify IT administration tasks
- 100% human reviewed database
- Mobile and Remote Filtering - Easily extend AUP and security policy enforcement to your mobile and laptop users
- Delegated Administration - Assign administrative tasks to others in your organization
Remote Filtering:
iPrism Web Security offers a Hybrid Remote Filter that employs proprietary technology to bring powerful Web filtering to all your users, regardless of their location, without using your VPN, deploying anything in the DMZ or requiring any PAC file implementations. iPrism Web Security eliminates browser latency while delivering secure and comprehensive Web access management to all your off-premises users.
Using a combination of the Remote Filtering Client for both Windows 32/64-bit and Mac, and powerful elastic data center cloud service, iPrism Remote Filtering, with centralized administration and reporting, is a true hybrid solution that allows you to enforce your corporate AUP across all employees whether they are on-premises or accessing your network remotely. And our unique hybrid technology keeps total cost of acquisition (TCA) and total cost of ownership (TCO) the lowest in the Industry.
iPrism Remote Filtering Delivers Simplicity, Value and Performance:
- Easy set-up and provisioning: Once you install the Remote Filtering Client software, you can manage and report on remote users easily from iPrism's browser-based central management console. And unlike solutions from other vendors, iPrism eliminates administrative burdens:
- No additional system modules to install off-box
- Eliminates the insecurity of copying users' directory service credentials off-premises
- No emails required to educate roaming users on self-provisioning
- Secure Client-Based Hybrid Technology: Unlike other vendors that rely on PAC file-based hybrid solutions, iPrism uses lightweight, low-latency, tamper-proof and application-agnostic client software. This eases the burden on IT Admin resources:
- Eliminates the need to restrict users' workstation privileges
- No need to restrict application usage
- No changes to or restrictions on users' browser proxy settings
- Accurate Off-Premises Policy Enforcement: The iPrism Remote Filtering client is location aware, which means you can apply and enforce the same or a different policy for roaming users, whether on- or off-premises relative to the corporate network. This also allows users to negotiate captive portals encountered at wireless hotspots such as airports, hotels, coffee houses and others.
- Centralized Administration and Reporting: Real-time monitoring and drill-down reporting work the same for your remote users as for those on-premises. You can run separate reports on remote users, isolate an individual remote user or include remote users in regular company-wide reports.
- Bandwidth Conservation - No Latency: Unlike other remote Web filters, iPrism helps conserve your bandwidth, because there are no VPN tunnels and no deployments in your DMZ to hog network bandwidth so low latency is assured.
- Distributed Data Center: A nationwide network of powerful, distributed data center cloud services supports iPrism's Remote Filtering so your users never encounter availability issues.
How iPrism Web Security Works
Our unique hybrid approach to remote filtering includes communications between the Web Filter and the Remote Filtering Client. The data center cloud service functions as a go-between, making sure the Web filter remain secure and conserving bandwidth.
iPrism Remote Filtering Establishes Policy
The iPrism Remote Filter defines policies for your remote users in accordance with your acceptable use policy (AUP). These policies are then pushed to the Data Center, where they are stored securely and confidentially to be applied to your remote clients once they are enabled.
iPrism Remote Filtering Enforces Policy
When a remote user accesses the Internet, the client software is connected to the data center and receives a disposition for the Web request based on its iGuard database URL rating and the profile that applies to the remote client. The data center tells the client to block or allow a site and to monitor or not to monitor the user's Internet activity.
iPrism Remote Filtering Sends Logs and Generates Reports
Periodically, the client sends logs of all your users' Internet activities on remote PCs or Macs to the data center. These logs are pulled on-demand and added to the local reports database. This gives you a single source of management reports for all users whether on or off-premises. Our unique technology allows you to compile reports from across your organization and drill down to a single user regardless of location.
Cloud Center:
The EdgeWave Secure Content Management Portfolio uses elastic in-the-cloud data centers that deliver proven resources to assure optimum scalability and availability of iPrism, EdgeWave's Email Security, Archiving, Hybrid Remote Filtering and other cloud-based services. In addition, cloud services deliver iPrism upgrades, iGuard URL updates and Circumvention Defense Network updates, including Bot detection. These proven data centers offer built-in failure resistance and redundancy, and are designed to isolate themselves from common failure scenarios. You can be certain that you will be able to enforce policies with your remote and roaming users as efficiently and accurately as you manage your on-premises employees.
Our Data Center Cloud Service Offers:
Elasticity - Cloud service data centers easily scale to handle the biggest pipelines and usage peaks so latency is never an issue.
Flexibility - Cloud services, are OS agnostic and will integrate seamlessly no matter what platform you are using
Reliability - Our in-the-cloud data centers have a proven infrastructure and a highly reliable environment where replacement instances are rapidly and predictably commissioned. With an SLA committed to 99.95% availability, you can count on accurate AUP enforcement for all employees 24/7/365, no matter where they are when they access your network.
Security - The cloud service data centers used by EdgeWave are committed to following security best practices including:
- Data Privacy - Your privacy is assured not only because of the built-in privacy and encryption capabilities, but because none of your organization's proprietary data is stored in-the-cloud. Once the client is deployed on your remote machines, event logs are stored there while iPrism does the URL monitoring and blocking. The in-the-cloud data service functions as a go-between enabling communication between your iPrism and the remote client.
- Physical Security - Distributed data centers are housed in secured locations with badge-only entrances and continuous video surveillance. This assures that only authorized, verified personnel have access to our data centers.
- Certifications and Accreditations - Data centers have successfully completed SAS70 Type II Audit, and will continue to obtain the appropriate security certifications and accreditations to demonstrate the comprehensive security of the infrastructure and services.